Sustainability | Free Full-Text | Probing Determinants Affecting Intention to Adopt Cloud Technology in E-Government Systems

Cloud Computing Adoption Theoritical Model 4. DISCUSION The intention... | Download Scientific Diagram
TekFinancial Solutions ® A Division of Tekmark ® Global Solutions, LLC Cloud Services Overview 100 Metroplex Drive Edison, NJ ph ppt download
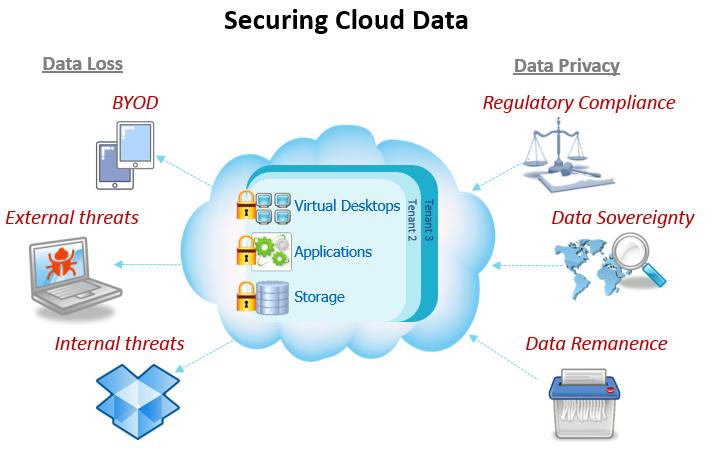
A Study on Key Integrity and Data Security Verification For Cloud Computing Environment - Ignited Minds Journals
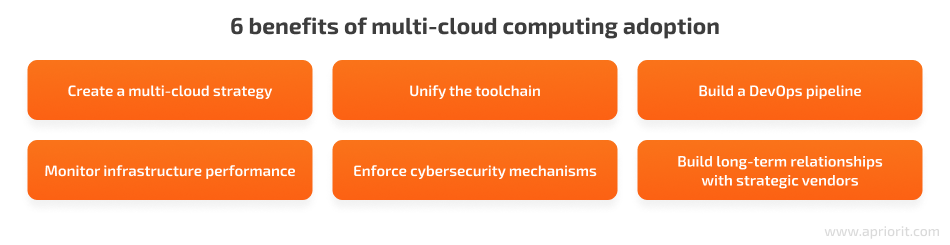
Module 5 Security Baseline Practices - 164 Cloud Computing Recovery—Find out what will happen to - Studocu
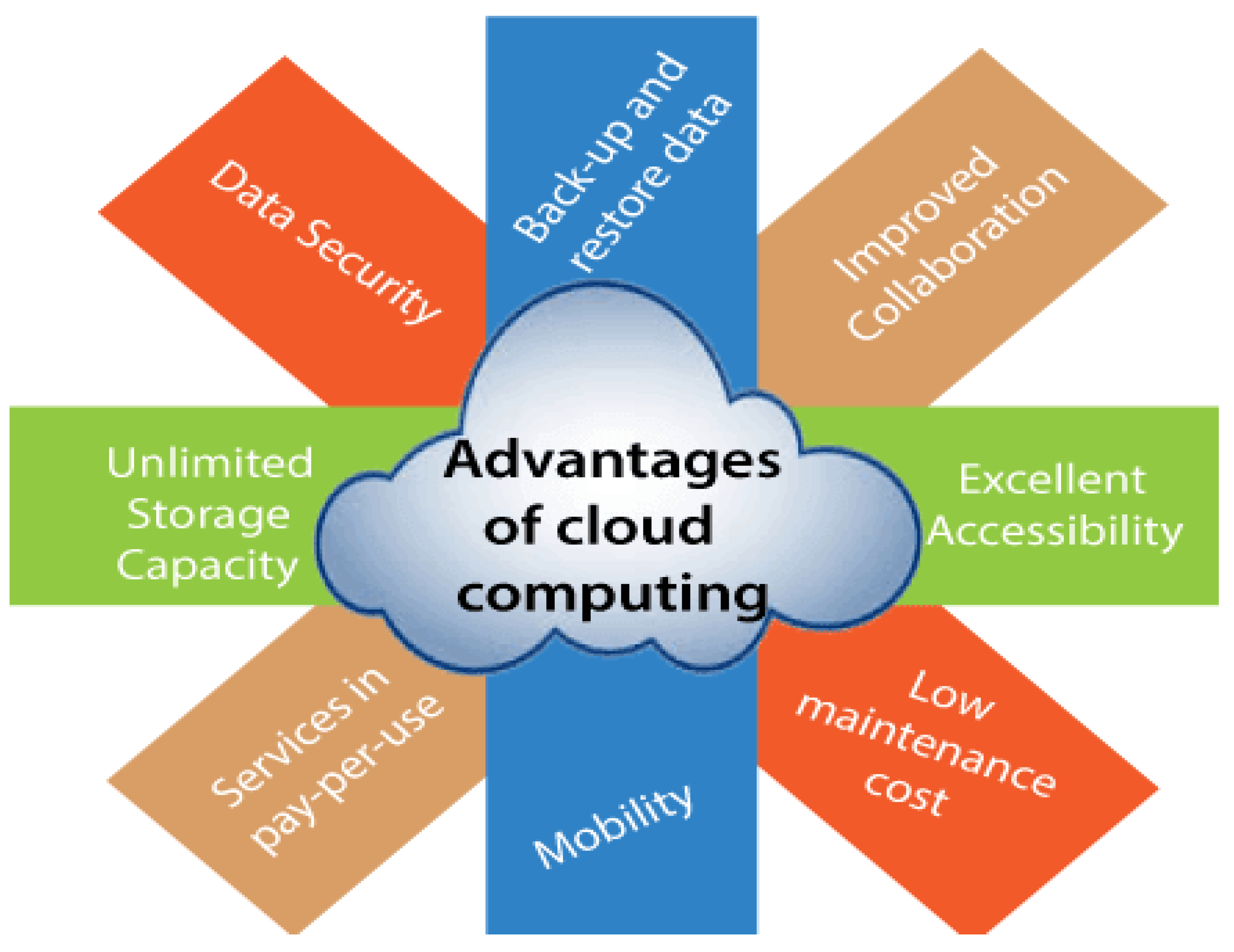
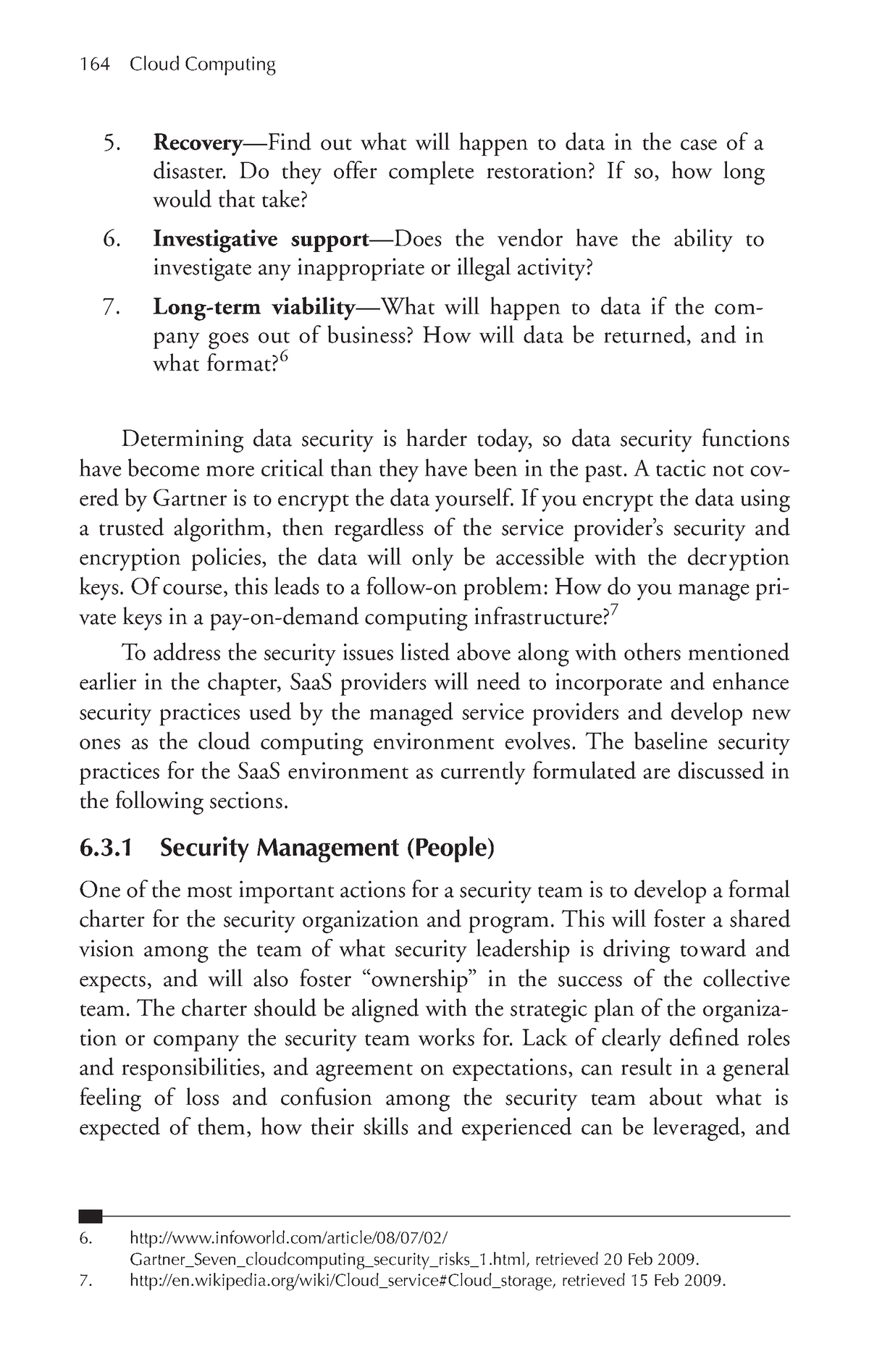
Applied Sciences | Free Full-Text | A Conceptual and Systematics for Intelligent Power Management System-Based Cloud Computing: Prospects, and Challenges










![PDF] Identifying Benefits and risks associated with utilizing cloud computing | Semantic Scholar PDF] Identifying Benefits and risks associated with utilizing cloud computing | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2d0e12b5b2d0736573d14f1bd8a6f7365e70ba58/4-Figure2-1.png)